Trusted Online Network 255941148 Guide

The Trusted Online Network 255941148 Guide outlines a framework for secure, accountable participation. It emphasizes governance clarity, verifiable credentials, and transparent practices. Core features include user verification, privacy controls, independent audits, and robust data handling policies. The guide aims for accessible language and concrete examples to support informed consent. It presents portable privacy tools and strong governance signals. For those evaluating online networks, its criteria point to measurable indicators—yet questions remain about implementation and real-world impact.
What Is the Trusted Online Network 255941148 Guide
The Trusted Online Network 255941148 Guide is a resource that explains the purpose, scope, and core features of the network.
It presents their framework, aims, and boundaries with a neutral tone.
It highlights trustworthy protocols and user verification as foundational elements, ensuring secure participation.
Clarity and freedom of action are preserved through defined standards, transparent practices, and accountable governance.
How to Evaluate Online Networks for Trust
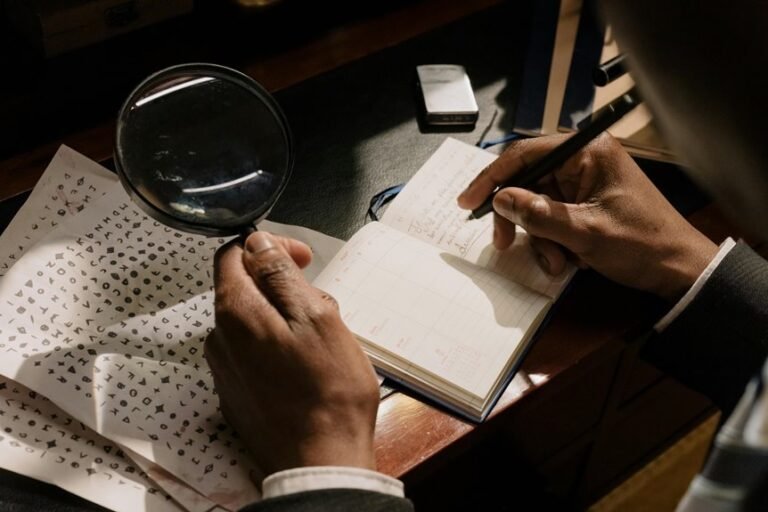
Evaluating online networks for trust involves assessing governance structures, verification mechanisms, and transparency practices established in the Trusted Online Network 255941148 Guide.
The evaluation focuses on governance clarity, accountable decision-making, and verifiable credentials, with attention to privacy controls and risk assessment.
It highlights independent audits, data handling policies, and disclosure of conflicts, enabling informed, freedom-minded users to compare network reliability and integrity.
Practical Steps to Protect Your Privacy Today
Practical steps to protect privacy today begin with a clear assessment of personal data exposure and the channels through which information travels.
The article emphasizes practical measures, not theory, focusing on portable controls and informed consent.
It highlights privacy practices that minimize data traces, secure devices, and limit sharing.
Emphasis on data sovereignty empowers individuals to govern how data is used and stored.
Building Reliable Connections Without Jargon
Building reliable connections without jargon centers on clear, direct communication that all parties can follow. The approach prioritizes accessible language, concrete examples, and documented expectations. It emphasizes consistency, feedback loops, and measurable signals over vague claims. The guide clarity emerges through precise terms and defined roles, while trust metrics track responsiveness, reliability, and alignment with stated commitments.
Conclusion
The guide defines a trusted online network as one with clear governance, verifiable credentials, and transparent data handling. In practice, it asks users to demand audits, portable privacy controls, and understandable terms. Critics note that real-world adoption hinges on independent verification and enforceable policies, not slogans. Still, the satire lands: a network that pretends to protect privacy while stamping “trust” on every banner—like a helper announcing, “We’ve modernized honesty, right after this privacy policy.”